How To Create A Jump Server In Windows
This blog post has been updated as of 03/30/2021.
Introduction
In this blog post nosotros'll cover how to set up up an SSH jump server. We'll comprehend two open source projects.
- A traditional SSH leap server using OpenSSH. The reward of this method is that your servers already have OpenSSH pre-installed. 2. A modern approach using Teleport, a newer open source culling to OpenSSH.
Both of these servers are like shooting fish in a barrel to install and configure, are free and open-source, and are unmarried-binary Linux daemons.
What is an SSH Jump Server?
An SSH jump server is a regular Linux server, accessible from the Cyberspace, which is used equally a gateway to access other Linux machines on a private network using the SSH protocol. Sometimes an SSH jump server is also called a "jump host" or a "bastion host". The purpose of an SSH bound server is to exist the only gateway for access to your infrastructure reducing the size of any potential set on surface. Having a dedicated SSH access bespeak also makes it easier to take an aggregated inspect log of all SSH connections.
Why non call information technology an SSH proxy? Partly due to historical reasons. In the before days of SSH, users had to SSH into a jump host and from there, they had to type ssh again to "jump" to a destination host. Today, this is done automatically using the ProxyJump option.
How to Set Upward an SSH Spring Server
A good security practice is to have a dedicated SSH jump server, i.e. not host any other publicly attainable software on it. Additionally, it is bad practice to permit users to log into a leap server directly. In that location are a few reasons why:
- Inadvertently updating the leap server configuration. - Using the jump server machine for other tasks. - Making copies of keys used to admission destination servers.
It is also a good idea to change the default TCP port on the SSH spring server from 22 to something else.
Allow'due south become over configuring an SSH jump server using two open up-source projects. We'll start with OpenSSH equally it's the nigh common.
Only first, let's make a few naming assumptions for the examples used beneath:
- The example organization domain is
example.com- The DNS proper noun of the jump server is going to beproxy.case.com
We'll likewise assume that proxy.instance.com is the only automobile accessible from the Internet.
OpenSSH
This SSH server comes bundled by default with most Linux distributions and there's nigh 100% adventure you lot already have it installed. If the server is accessible via proxy.example.com so you tin can admission other servers backside the same NAT boundary via -J command line flag, i.e. on the customer:
$ ssh -J proxy.example.com 10.2.ii.i
In the instance in a higher place, the jump server is used to access another host on an AWS VPC with an accost of 10.2.2.one. So far, this looks pretty piece of cake.
To avoid typing -J proxy.example.com all the time, you can update your client's SSH configuration in ~/.ssh/config with the post-obit:
Host 10.two.2.* ProxyJump proxy.instance.com Now, when a user types ssh 10.2.2.1 their SSH client will not even try to resolve 10.2.two.1 locally, but instead will establish a connection to proxy.example.com which will forrad information technology to 10.2.2.one within its VPC.
Next, we need to harden the server configuration a fleck by disabling interactive SSH sessions on the bound server for regular users, simply leaving it turned on for the administrators. To do this, update the sshd configuration, commonly in /etc/ssh/sshd_config with the following:
# Exercise not let SSH clients do anything except be forwarded to the destination: PermitTTY no X11Forwarding no PermitTunnel no GatewayPorts no ForceCommand /sbin/nologin The example above volition work for Debian and its derivatives, we propose to verify the existence of /sbin/nologin.
This volition piece of work for every bit long equally the jump server has accounts for all SSH users, which is inconvenient. Instead, consider creating a split user business relationship on the leap server defended to "jumping users". Permit's call it jumpuser and update the configuration:
Lucifer User jumpuser PermitTTY no X11Forwarding no PermitTunnel no GatewayPorts no ForceCommand /usr/sbin/nologin And the users will accept to update their client SSH configuration with:
Host 10.ii.two.* ProxyJump jumpuser@proxy.example.com For more information on how to fine-tune SSH jump configuration to your particular state of affairs, consult homo ssh_config and man sshd_config.
Needless to say, the setup above works only when the public SSH keys are properly distributed non simply between clients and the bound server, but also betwixt the clients and the destination servers.
Teleport
Teleport is a much newer SSH server, which was released in 2016. Unlike OpenSSH, Teleport is a highly opinionated SSH implementation:
- It insists on using an SSH proxy by default, and its SSH proxy has a spider web-based interface, allowing users to SSH using a browser.
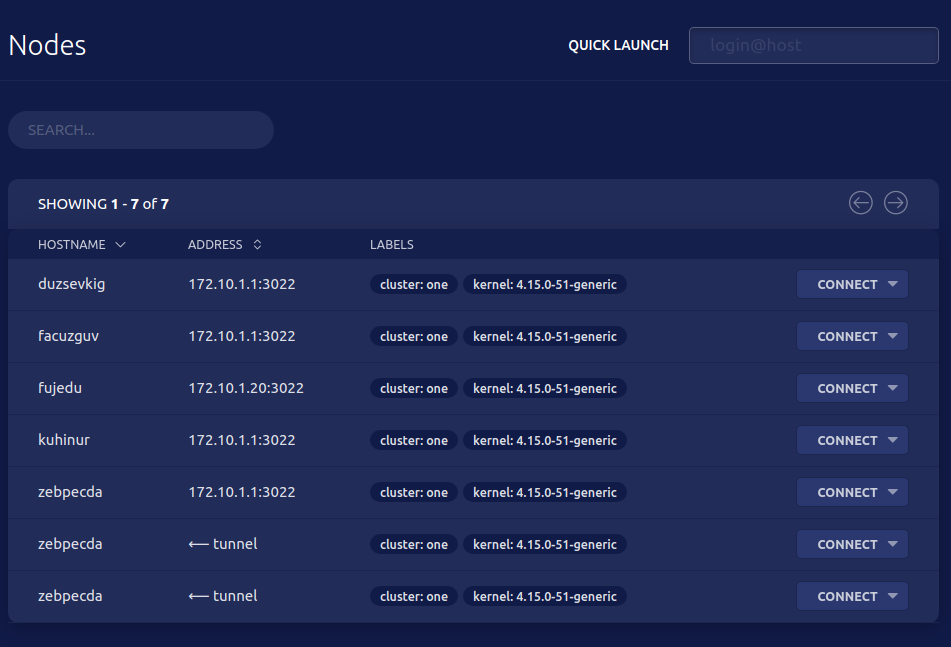
- Dissimilar traditional SSH servers, Teleport removes the need to maintain "inventories" of servers as it offers a live introspection, i.e. y'all can list all online servers behind a proxy as shown in this screenshot:
In improver to having a modern proxy functionality, Teleport offers a few advantages over traditional SSH:
- It does not use SSH keys and instead defaults to more secure and flexible SSH certificates. This removes the demand for primal management and makes SSH servers completely stateless and configuration-free.
- It supports other protocols in improver to SSH, so the same "jump host" tin exist used to access other resource behind NAT, such equally Kubernetes clusters or even internal applications via HTTP(s).
- Teleport does not rely on Linux users for hallmark. Instead, it maintains a separate database of users or can integrate with a unmarried sign-on with other identity providers such as Github, Google Apps, or enterprise options such as Okta and Agile Directory.
Teleport always comes with a proxy (i.east. the same thing as a "jump server") and there are no special instructions for setting information technology upwards. We suggest you get-go by downloading Teleport for your platform and follow the quick starting time guide.
Teleport cybersecurity blog posts and tech news
Every other week we'll send a newsletter with the latest cybersecurity news and Teleport updates.
Conclusion
In this blog post we covered how to fix upwards an SSH leap server using ii open-source projects: OpenSSH and Teleport. Which one should you choose?
Use OpenSSH if:
- The number of servers or/and users in your organization is small
- You need a jump host setup quickly and do not accept much time to learn new tech
Use Teleport if:
- Your server fleet or the size of your team is growing
- You lot need to connect to servers located "in the wild", i.due east. non restricted to a single VPC
- Y'all accept a couple of hours to play and learn a new tool
- ssh
Source: https://goteleport.com/blog/ssh-jump-server/
Posted by: emerydespassoling.blogspot.com

0 Response to "How To Create A Jump Server In Windows"
Post a Comment